Setting up a hacking lab with Kali Linux and Metasploitable, Part 1 | The Best C# Programmer In The World - Benjamin Perkins
Setting up a hacking lab with Kali Linux and Metasploitable, Part 1 | The Best C# Programmer In The World - Benjamin Perkins

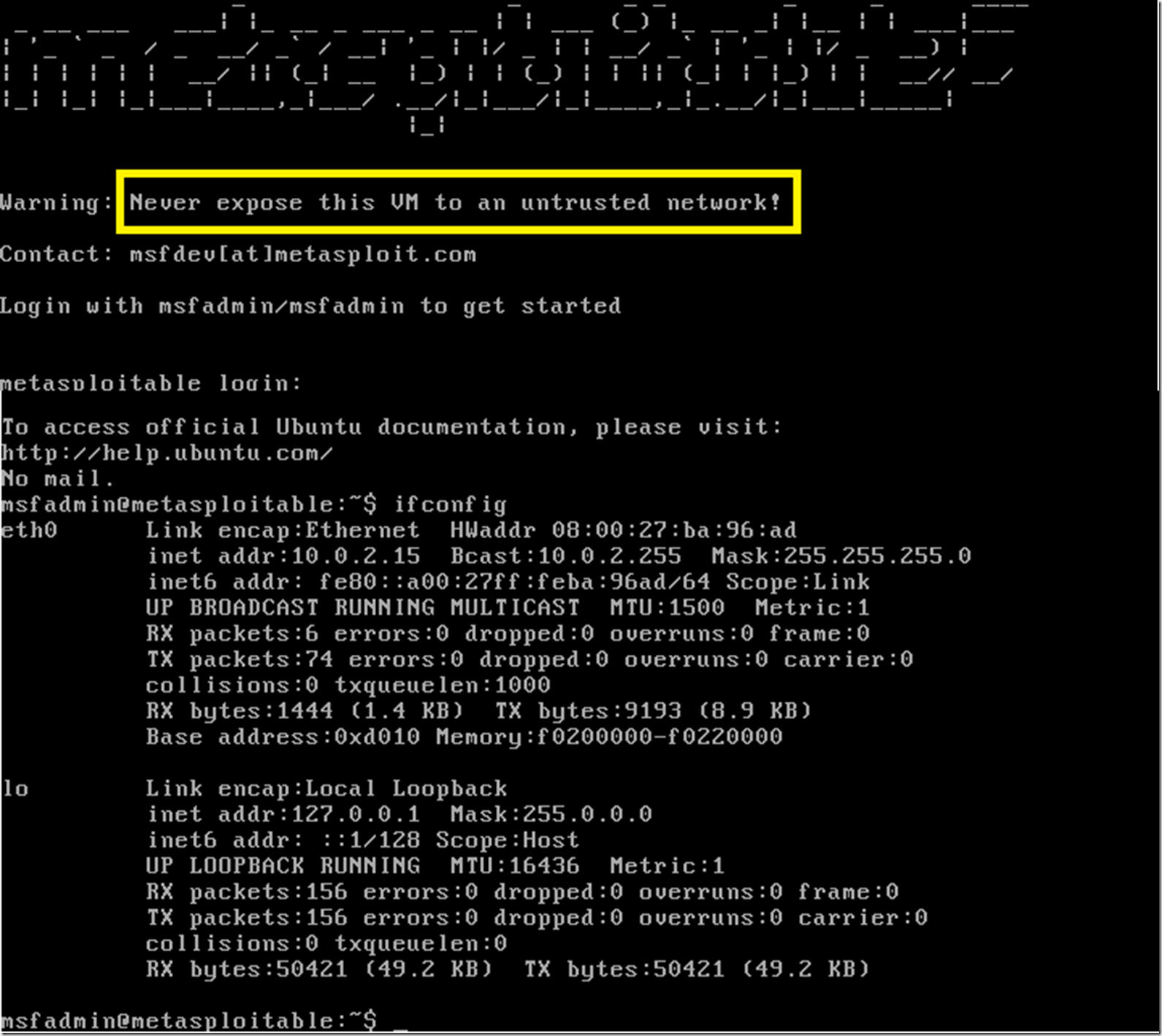
Metasploitable 2 Linux – Most Vulnerable OS in the town : Introduction and Installation | Information Treasure
Setting up a hacking lab with Kali Linux and Metasploitable, Part 1 | The Best C# Programmer In The World - Benjamin Perkins

Metasploitable 2 Linux – Most Vulnerable OS in the town : Introduction and Installation | Information Treasure
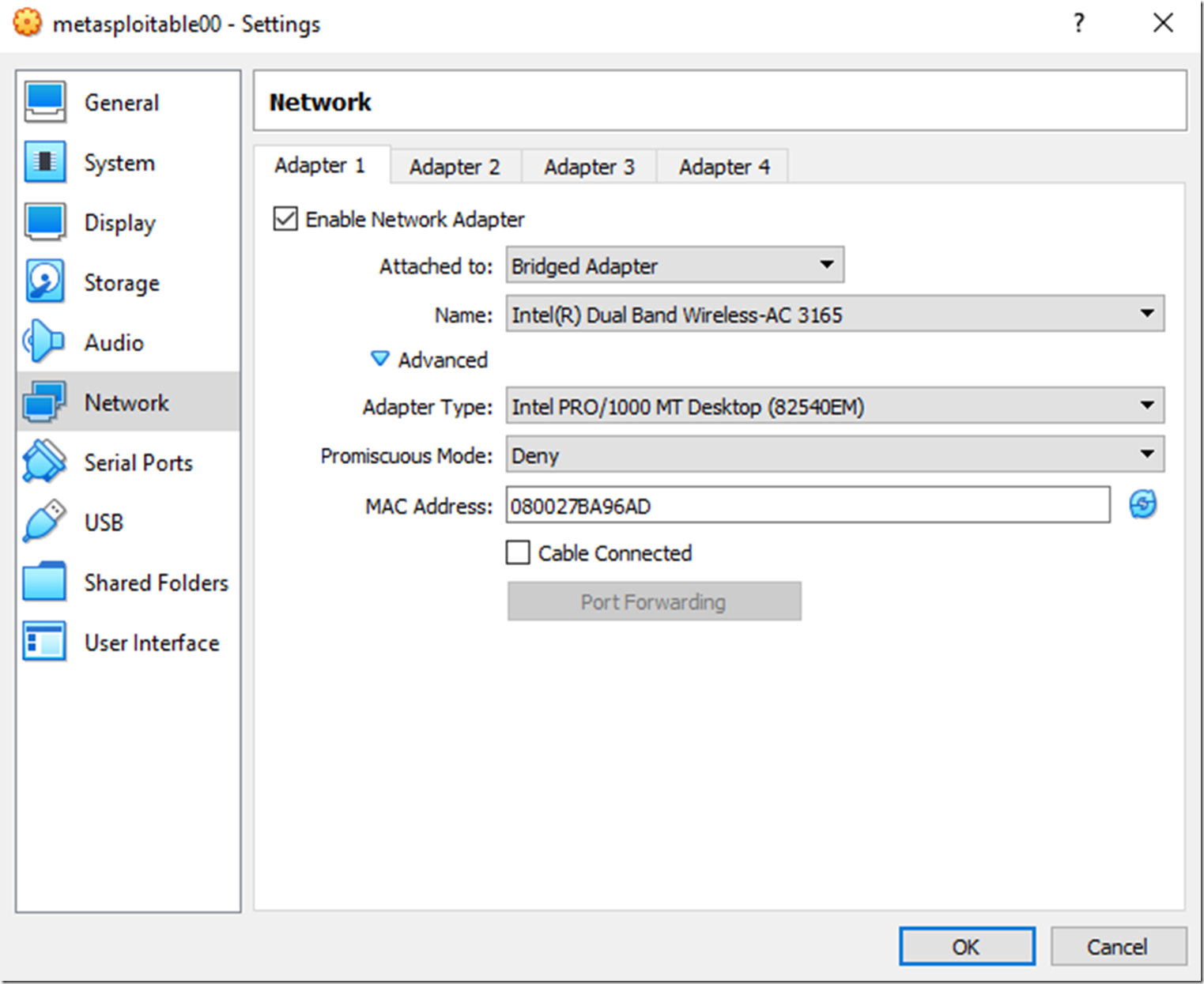
Setting up a hacking lab with Kali Linux and Metasploitable, Part 1 | The Best C# Programmer In The World - Benjamin Perkins
Setting up a hacking lab with Kali Linux and Metasploitable, Part 1 | The Best C# Programmer In The World - Benjamin Perkins











![Setup Hacking Lab with Metasploitable [7 Easy Steps] | GoLinuxCloud Setup Hacking Lab with Metasploitable [7 Easy Steps] | GoLinuxCloud](https://www.golinuxcloud.com/wp-content/uploads/meta-2.jpg)